Despite the mystery and intrigue surrounding the dark web, it’s not much more than a small part of the deep web.
And getting on the dark web is easier than you think – you really only need two tools: the Tor Browser and a reliable, Tor-friendly VPN.
But you also need to know how to use these tools properly.
Otherwise, you won’t be safe on the deep or dark web.
And speaking of deep vs. dark web, the media is constantly getting them confused!
But I’ll clear it up for you in a bit.
Ready to dive below the surface?
How to Browse the Dark Web Safely – TL;DR
If your curiosity is overwhelming and you can’t wait any longer, this TL;DR version of how to browse the dark web safely is for you!
- Choose a reliable, Tor-friendly VPN and purchase a subscription before installing the VPN app.
- Install the Tor Browser on your device.
- Connect to your favorite Tor-friendly VPN server.
- Open the Tor Browser and connect to the Tor Network.
- Find a dark web website using an aggregator, or dip your toes by starting with the .onion version of well-known, legitimate sites.
It’s as easy as that!
But it’s also just as easy to get something wrong.
So, to make sure you’re browsing the dark web safely, read my in-depth tutorial below ASAP!
In-Depth Tutorial on Surfing the Dark Web Safely From Any Device

Now you know the basics.
But, as I said, it’s too easy to make a mistake if you don’t know how to apply those basics properly!
Luckily, that’s what I’m here for.
However, before we start, it’s important to clarify that I’ll be referring to the dark web (vs. deep web) as we go along.
This will make everything easier to understand.
But don’t worry!
Later on, I’ll explain the differences between the two.
For now, though, let’s start by looking at how to surf the dark web from any device safely!
Step 1: Download a Reputable VPN

It’s entirely possible to access the dark web without using a VPN.
But it’s not safe to try that route – so your first step should always be choosing and downloading a reputable VPN!
I’ll walk you through three of my favorites to use when surfing the dark web from any device a little later.
That way, you can choose the one that works best for your needs.
In the meantime, here’s how to download the VPN you choose for accessing the dark web.
Read Also: Best VPNs for the Dark Web
For Computers
If you want to safely access the dark web on your computer, downloading the VPN app is super easy!
Here’s what to do if you use Windows or Mac:
- Visit your preferred VPN provider’s website through your regular browser and choose one of their subscription plans.
- Create your VPN account and pay for your subscription.
- Click on the download link your VPN provider gives you.

- Choose where to save the download file and wait for it to finish downloading.
It’s as easy as that!
The download process is essentially the same if you use Linux, though you can also download and install your VPN using terminal commands.
However, this isn’t the best way, as using the terminal means downloading your VPN through its repository.
Most of the time, these repositories are for an older version.
So, to get the most recently updated version of your chosen VPN, you should always download the app directly from the website.
Different Linux distributions sometimes have different download processes, too.
When in doubt, follow the on-screen instructions your VPN provider gives you!
For Android
Want to surf the dark web from your phone instead?
Here’s how to download your VPN app on Android devices!
- Visit the VPN provider’s website through your browser app and choose one of their subscriptions.
- Sign up by creating your user account and purchase the subscription you chose.
- Your VPN provider will give you two options for downloading their Android app:
- A Google Play Store link – you should get the app through this link to make sure you don’t accidentally download a fake version from the Play Store;
- An APK download file – if you choose this option, make sure to enable your phone’s “Install Unknown Apps” setting for your browser app!
- Tap the Download button.
- Wait for the download to finish.
- Google Play Store downloads will automatically install as part of the download process.
- APK downloads will ask you if you want to install the app after your phone finishes unpacking the APK at the end of the download process.
If you’ve never used APK downloads before, I recommend sticking to the Google Play Store method for now.
For iOS
Downloading your VPN app on an iPhone or iPad is similar to the Google Play Store method on Android.
Just follow these easy steps:
- Visit the VPN provider’s website through your browser app and choose one of their subscriptions.
- Sign up by creating your user account and purchase the subscription you chose.
- Your VPN provider will give you a link to download their app from the Apple App Store.
- Apple is very strict about the apps available in the App Store, so it’s less likely you’ll find fake versions there. But better safe than sorry – follow the link on your VPN provider’s website!
- Tap the Download button.
- Wait for the download to finish. The app will automatically install.
Now you’re ready to start setting up your VPN!
Step 2: Install & Set Up Your VPN
Once your VPN app (or desktop client) is finished downloading, you need to install and set it up before using it.
Luckily, this is a once-off process for each device!
For Computers
On a Windows or macOS desktop or laptop computer, install your VPN by:
- Double-clicking the download file.

- Following the on-screen installation instructions.

- Letting the installation process complete.
It’s that easy!
With Linux, installations might require you to use the terminal app.
As always, follow your VPN provider’s instructions for installing the app on your Linux distribution or check out this video with step-by-step instructions:
Now it’s time to set up your VPN:
- Double-click on the desktop shortcut if the app doesn’t automatically launch at the end of the installation process.
- Log in to the app using the username (or email address) and password you set when creating your VPN account.
- Open the app settings menu.
- It’ll be the cog icon in some apps – otherwise, look for the burger (three lines) or three-dot option. Sometimes, it might even be a toolbar option called “Settings!”

- Look for the kill switch setting to make sure the feature is enabled. If not, enable it before connecting to a VPN server.
- In some VPN apps, the kill switch is in the General tab. For others, it’s under the Connection (or similar) tab or in its own separate tab.

- Choose a VPN server near you and connect by clicking on it.
- All of the VPNs I recommend later in this guide have a quick or smart connect option – click on it to save time instead of manually choosing a server.
- NordVPN has the Onion Over VPN option as well. Click on it to connect to a server that’s optimized for surfing the dark web.

- Run a quick IP, DNS, and WebRTC leak test.
That’s it – you’re ready to move on to the next step!
For Android and iOS
To set up your VPN on Android and/or iOS, follow these easy steps:
- If the VPN app doesn’t automatically open, tap on its icon.
- Log in to your account using your username (or email address) and password.
- Tap on the three dots, cog icon, or burger menu (three lines) and choose Settings.
- Make sure your VPN’s kill switch is enabled.
- Similar to the desktop app, your VPN’s kill switch will either be under General or Connection settings. However, some, like NordVPN, have it enabled by default with no option to disable it.
- After exiting the Settings menu, tap on the Quick Connect or Smart Connect button, or manually choose a VPN server near your location.
- Don’t forget, NordVPN has specialized Onion Over VPN servers! Choose one of these for accessing the dark web.
- Run a quick IP, DNS, and WebRTC leak test.
You’re almost ready to surf the dark web through your phone!
Step 3: Choose an Overlay Network
You can’t access the dark web through your regular browser, so you’ll need to choose an “overlay network.”
Overlay networks are a special kind of browsing tool.
There are a few options, but the two most popular are Tor Browser and Freenet.
You can actually use Freenet through Tor Browser.
I don’t recommend this method, though, as it introduces too many security issues.
It’s always best to keep things as safe and straightforward as possible.

And, in any case, I find Tor to be the best overlay network – and the easiest to use.
This is why I recommend Tor over Freenet.
It’s also 100% free to use on any device.
All you need to do is download and install the app from the website – torproject.org.
VERY IMPORTANT!
Always download your overlay network directly from the official website!
But just in case you prefer Freenet, I’ll show you how to set up both overlay networks in the following sections.
Download the Tor Browser for Windows, macOS, or Linux
Downloading the Tor Browser on a computer is very easy, no matter your operating system.
Just follow these steps:
- In your regular browser, visit torproject.org and download Tor Browser for Windows, macOS, or Linux.

- Save the installation file to your preferred location on your computer.
- Double-click on the installation file (.exe for Windows, .dmg for macOS, and .tar.xz for Linux).
- For Windows and macOS, follow the on-screen installation wizard’s instructions.
- For Linux, the terminal command line method works best. Follow the official installation Linux instructions for Tor here.
Once the installation process is complete, you’re ready to start setting up your overlay network.
Download the Tor Browser for Android
Although there’s a Google Play Store entry for the Tor Browser’s Android app, you’re always safer going the slightly longer way around.
Follow these steps to download and install Tor on your Android smartphone safely:
- Visit torproject.org through your regular browser app and tap on the Download for Android button.

- Tap the Go to Google Play button and tap Download.

- Alternatively, if you use F-Droid to download open-source apps, tap on the Go to F-Droid button instead.

- Remember, you’re downloading the Tor Browser APK through F-Droid, so you need to enable your phone’s “Install Unknown Apps” setting for F-Droid.
- Tap the Download button.
- Wait for the download to finish.
- Google Play Store downloads will automatically install as part of the download process.
- APK downloads will ask if you want to install the app after your phone finishes unpacking the APK at the end of the download process.
Once you’re done, you can skip ahead to setting up your overlay network!
Download the Onion Browser for iOS
Apple has strict rules for all iOS web browsing apps to follow, including overlay networks like Tor.
For this reason, iPhone and iPad users can’t use the real Tor Browser app.
Instead, the Tor Project has a separate overlay network for iOS users.
Follow these steps to download and install it:
- Visit onionbrowser.com through your regular browser app, and tap the Download on the App Store button.

- Tap Download.
- Wait for the download to finish. The app will automatically install.
IMPORTANT REMINDER!
It’s crucial to download the Onion Browser on your iOS device by going through the website.
There are many other Tor Browser alternatives in the App Store, but the Onion Browser is the ONLY one that the Tor Project recommends!
Now it’s time to set up your overlay network!
Step 4: Set Up Your Overlay Network Client

Just like you had to set up your VPN app before connecting, it’s best to make sure your overlay network client is adequately set up for safely accessing the dark web.
As promised, I’ll also include the steps you should follow for setting up the Freenet overlay network.
But first, let’s look at the Tor Browser…
Tor Browser: Best Config Setup for Safety (Windows, macOS, and Linux)
Ready for some great news?
No matter what operating system your computer runs on, the setup process for Tor is the same!
- If the Tor Browser didn’t automatically launch when it finished installing, double-click on the desktop shortcut.
- Click Tor Network Settings on the start-up page.

- In the Privacy & Security tab, scroll to Security > Security Level and click on Safest to enable the highest security configuration.

- In the Search tab, you can also change the default search engine from DuckDuckGo to DuckDuckGoOnion. This routes your search queries through DuckDuckGo’s .onion domain, adding an extra layer of privacy to your searches through the Tor Browser.
- In the Tor Browser URL Bar, type about:config and hit Enter.

- Click “Accept the Risk and Continue.”

- Disable HTTP Referrers by searching “network.http.sendRefererHeader” and changing the value to 0.
- This stops websites from seeing how you reach them, for example, through a link on another site or via the search page.

- Disable iframes by searching “noscript.forbidIFramesContext,” selecting “Number,” and changing the value to 0.
- iframes adds links inside of links, so they can easily be abused to spread malware – especially when surfing the dark web.

- Save your configuration settings by clicking Connect on the Tor Browser’s start page or your config settings page.

- Even though you already did so using your regular browser, run another quick IP, DNS, and WebRTC leak test.
There you have it – you’re just one step away from accessing the dark web on your computer!
Tor Browser: Best Setup for Safety on Android
The Tor Browser app for Android is still relatively new – it was only launched in 2018.
So, it’s understandable that it’s more difficult to find a guide for the best Tor Browser setup for safety on Android.
But, lucky for you, the most in-depth one is right here!
Just follow these steps.
- Open your Tor Browser app by tapping on it.
- Tap Connect and wait a few moments until the screen updates.
- Tor immediately gives you the option to Set Your Security Level without opening the security settings. Take advantage by tapping Safest.
- Tap the three dots on the bottom-right of your screen, then open the Settings menu.
- If you prefer, you can move the toolbar (with the search bar and three-dot-menu) to the top like other browser apps by changing the setting in the Customize tab.
- Open the Search tab and change the default search engine from DuckDuckGo to DuckDuckGoOnion.
- Even though you already did so using your regular browser, run another quick IP, DNS, and WebRTC leak test.
Once you finish, you’re unbelievably close to safely browsing the dark web on your Android device!
Onion Browser: Best Setup for Safety on iOS
The Onion Browser is not the best or safest way to use the Tor overlay network for browsing the dark web.
However, unfortunately, it’s the only option for iPhone and iPad users.
If you still want to give it a try, follow these steps:
- Open your Onion Browser app by tapping on it.
- You can choose to use a bridge or continue without.
- Using bridges is recommended in countries where Tor is restricted but not necessary otherwise.
- Tap Connect to Tor and wait a few moments until the screen updates.
- Wait for the Onion Browser to finish connecting, then choose your Security Level. I recommend either Silver or Gold. After you choose, tap “Start Browsing.”
- The updated screen will confirm that you’re connected to Tor.
- Even though you already did so using your regular browser, run another quick IP, DNS, and WebRTC leak test.
The Onion Browser is far from ideal, but that’s entirely thanks to Apple’s policy of policing what iOS users can and cannot do on their own devices.
Fortunately, if you use the settings above, you’ll be as safe as possible for browsing the dark web on an iOS device.
Freenet: Best Config Setup for Safety

I strongly prefer using Tor instead of Freenet, but some of you might feel otherwise.
Still, it’s important to note that Freenet doesn’t offer any dedicated overlay network apps.
Instead, you install the overlay network package, which then runs in your regular browser.
This is far from ideal, as you really want to keep your darknet browsing 100% separate from your regular browsing.
But if you want to use Freenet on Windows, macOS, or Linux, follow these steps for the best config setup:
- Once your Freenet installation is complete, double-click on the Browse Freenet shortcut that appears on your desktop.
- Your default browser will launch in an incognito tab with a screen asking you to set your security level. Unfortunately, to browse most content using Freenet, you’ll need to use Connect to Any Freenet User (also known as opennet), which has low security.
- If you know other Freenet users and only want to access the content they host on their nodes, you can choose the Connect Only to Friends (also known as closednet).
- For the utmost security, when prompted to protect your “downloads, uploads, and Freenet browsing cache,” choose “MAXIMUM.” This will set a temporary encryption key that wipes downloads, uploads, and cache upon restarting Freenet.

- Because Freenet is a Peer-to-Peer (P2P) network, you’ll be asked to set the storage space you want to contribute. The minimum is 512 MiB.

- Next, Freenet asks you to set a Transfer Limit. For the best results, select the option that is 50% or less of your internet connection’s best results.

- You can now start browsing the Freenet p2p network.
I strongly recommend having a separate browser that you only use Freenet with.
Otherwise, you aren’t browsing Freenet content safely – even if you use the closednet option and a VPN!
Step 5: Figure Out What Kind of Websites You Want to Browse

Contrary to popular belief, you won’t only find illegal sites on the dark web (though there’s plenty of those, too)!
In fact, you can find some of the same sites on the dark web that you can visit usually.
The only difference is that the dark web versions are .onion sites instead of .com or .org (etc.).
Either way, you know better than I do what kind of websites you want to browse on the dark web!
My one huge disclaimer is that I do not suggest, encourage, or condone browsing dark web websites that host illegal content or provide unlawful services!
Step 6: Finding the Dark Web Site You’re Interested In
Websites on the dark web don’t just use the .onion TLD (Top-Level Domain).
In fact, sometimes the .onion is the only part of a dark web website’s URL that makes sense!
This means you can’t simply replace .com with .onion and expect it to work.
You’ll need to find reputable aggregator lists to find .onion links.
Some aggregator sites are only accessible through Tor, but they tend to list sites with illegal content as well.
It’s also worth noting that most lists you find will have the v2 Onion links, which no longer work as of October 15, 2021, when v3 Onion became the only supported option.
Luckily, there are already some that updated their lists to include the v3 Onion links!
Some Dark Web Sites You Might Be Interested In
Here are some dark web websites you might be interested in.
I’ve made sure only to include the updated v3 Onion links.
Only follow these links through the Tor Browser while connected to your VPN:
- The Hidden Wiki – it’s Wikipedia, but on (and for) the dark web! Just… be careful what you click on because there are illegal sites indexed on The Hidden Wiki too.

- Daniel – easily the best dark web website aggregator for quickly and easily finding the type of sites you’re interested in. But, again, be careful what you click on.

- Dread – the dark web’s version of Reddit.

- Beneath VT – interested in the steam tunneling beneath Virginia Tech? This is the dark web website where you can read all about it.

- ProPublica – that’s right, you can keep up with the news on the dark web too! ProPublica launched their .onion site so people in countries with heavy government censorship can still access their content.

- Elude – a free, encrypted email service that is perfect for creating an anonymous email account for any dark site subscriptions (like creating a Dread account).

- ProtonMail – yes, you can even use ProtonMail on the dark web! The Swiss email provider actually strongly recommends whistleblowers and journalists sign up for a free (or premium) ProtonMail account via their .onion site. Though, at the time of writing, I could only get an endless loading screen.

- SecureDrop – a p2p file-sharing platform designed for whistleblowers to use for anonymously sharing leaked documents.

- QubesOS – interested in trying out a Linux distribution designed with security through isolation in mind?

There are a few that I’ve left off this list.
Some, like Facebook’s .onion site, I don’t recommend unless you created your account there (instead of at Facebook.com).
Others, like Hidden Answers and Intel Exchange, no longer exist or aren’t loading.
Remember to only click on the links above while using your VPN and Tor!
What Are the Best VPNs for the Dark Web?
Now that you know how to set up your VPN and use Tor to access the dark web let’s look at the best VPNs for the job!
1. NordVPN – Onion Over VPN

My favorite VPN to use when browsing the dark web is NordVPN, as it’s the only reputable VPN provider that offers dedicated servers for accessing the Tor Network.
These specialized servers are easily identified in NordVPN apps by the heading Onion Over VPN.

Even if you forget to click on the Onion Over VPN heading when looking for a NordVPN server, its regular server list makes finding them easy.
Just look for the servers with a small onion icon next to them!
If, for whatever reason, you end up not using the Onion Over VPN servers, NordVPN also has a backup solution: its Double VPN feature.
NordVPN’s Double VPN routes your traffic through two of its VPN servers, and this adds a second layer of encryption and changes your IP address twice.
So, by the time you connect to the Tor Network, it’s virtually impossible to identify you!

Now, using the Tor Network (even for browsing regular sites) is rather slow.
And usually, adding a VPN to the connection makes it even slower.
But that’s not the case with NordVPN!
Thanks to its blazing-fast, highly secure proprietary VPN protocol, NordLynx, the only reason your connection will be slower than usual is because of the Tor Network!

Best of all, many of NordVPN’s servers include obfuscation to help hide that you’re using a VPN at all, adding yet another layer of anonymity and privacy to your connection.
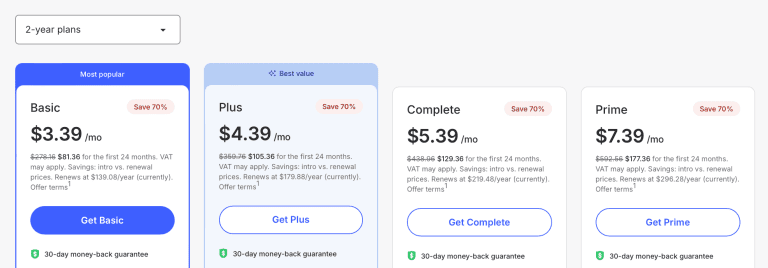
NordVPN’s subscription plans are also very affordable.
Pros
- Onion Over VPN servers
- Double VPN (as a backup)
- Obfuscation (some servers)
- Blazing-fast (with NordLynx)
- Kill Switch
Cons
- Specialty connections like Onion Over VPN are slower than regular NordVPN server connections
2. ExpressVPN - Premium Obfuscation

ExpressVPN is another excellent VPN to use when browsing the dark web.
Its biggest advantage over NordVPN (and Surfshark) is that it offers automatic obfuscation on all of its servers – no matter what VPN protocol you’re using!
This means you can use ExpressVPN’s proprietary protocol, Lightway, for the best possible speeds when using Tor to browse the dark web.
So, while ExpressVPN doesn’t offer a double VPN feature, I feel its automatic obfuscation makes up for it.
That said, ExpressVPN is more expensive than most VPNs:
Pros
- Automatic obfuscation on all servers (OpenVPN and Lightway)
- Blazing-fast (with Lightway)
- Kill Switch
Cons
- More expensive than other VPN providers
- No Double VPN/MultiHop features
3. Surfshark – Lightweight Obfuscation

Surfshark is my final favorite – not least because its lightweight obfuscation feature ensures your connection remains private at all times without sacrificing speed!
That’s right.
If you use the OpenVPN protocol, Surfshark’s Camouflage Mode automatically kicks in to hide that you’re using a VPN and browsing the dark web with Tor (or Freenet)!
Surfshark also offers an even more robust obfuscation setting, NoBorders Mode!
This one is specially designed to help users access the free web worldwide, making it especially handy for users in countries where Tor is restricted or banned.
Surfshark also has a MultiHop feature.
This is its version of NordVPN’s Double VPN, so your connection goes through two Surfshark servers instead of one.
Best of all, Surfshark’s subscription plans are affordable:
Pros
- MultiHop
- Automatic Camouflage Mode obfuscation
- Optional NoBorders Mode obfuscation
- Blazing-fast
- Kill Switch
Cons
- Obfuscation currently only available with OpenVPN connections
- MultiHop slows your connection speed
Why Do You Need a VPN for the Dark Web?

There are several reasons you need to use a VPN for surfing the dark web:
- Without a VPN, your ISP can see you’re using Tor – even though they don’t know what you’re using Tor for. But because it’s well-known that Tor is used for accessing the dark web, identifying Tor usage can raise suspicions.
- Your ISP might throttle your bandwidth connection while you’re using Tor. Or they might block Tor connections altogether, especially if Tor is censored in your country.
- Even though it’s difficult to do, ISPs and government agencies can sometimes determine which sites you’re visiting through the Tor Browser. They do this by monitoring websites accessed through Tor, then correlating the timestamps for traffic coming through a Tor exit node with outbound traffic to entry nodes.
- In the same way, dedicated cyber criminals on the dark web can also use correlation attacks to identify you. They’ll use slightly different methods, but they can use that information to launch a cyberattack once they identify your real IP address.
Using a VPN hides that you’re using Tor at all.
At most, your ISP will see that you’re connecting to the internet through a VPN tunnel.
And if your VPN uses obfuscation, your ISP won’t even know that!
A VPN also changes your IP address before you connect to the Tor Network, making it even more difficult for anyone to figure out your real IP address.
Dark Web vs. Deep Web
As I mentioned earlier, the media usually doesn’t differentiate between the dark web and the deep web.
I can understand why.
After all, the difference might seem trivial to most people – especially if they have no experience with either!
But if you want to be 100% accurate, you have to understand that the dark web and deep web aren’t exactly the same thing.
Technically speaking, the dark web is a very small part of the deep web.
Take a look at the table below for a quick explanation of the differences:

WEB TYPE | WHAT IS IT? |
Surface or Clear Web | The regular web – everything you can access through your normal browser and a search engine. Surface or Clear Web content doesn’t require login access and can be indexed by web crawlers. |
Deep Web | The deep web makes up most of the content online. These web pages (and sometimes even whole websites) aren’t indexed by web crawlers and usually require login access. You can still access most of the deep web through your regular browser. |
Dark Web | The dark web is the part of the deep web that is purposefully hidden and can only be accessed through an overlay network like the Tor Browser. Dark web websites have special URLs that end with the .onion TLD. You need to use an aggregator site to get dark web links because web crawlers don’t index these sites. You can’t even find them using the .onion version of DuckDuckGo in the Tor Browser! |
What Is the Deep Web?
The deep web is anything and everything online that you can’t find using a search engine.
This is because dark web pages (and sometimes whole sites) block search engine crawlers that index online content to make it searchable.
Most online content (whether stored in centralized servers or on a distributed P2P network, like blockchains) actually belongs to the deep web.
You can access most of the deep web using your regular browser.
The only difference is, you’ll almost always need to log in to an account to access the content.
For example, if you use cloud storage – like DropBox, AWS, or Apple’s iCloud – you’re using the deep web.
Doesn’t sound so scary anymore, does it?
And it shouldn’t be.
The deep web is an important part of the internet.
Without it, private information like court records and business intranets (the backend side of things that only employees can access) would be out in the open.
The deep web is also great for finding research papers.
That’s what aggregator sites like Archive.org and the Library of Congress are for!
One issue you might run into when looking for research papers this way is that many deep web websites hide this content behind payment walls.
For example, JSTOR charges $200 a year for access to 10 PDF downloads per month.
Luckily, there’s a free workaround… the Unpaywall browser extension.
If there’s a free version of the paper somewhere else online, Unpaywall will help you find it.

What Is the Dark Web?
The dark web is a very small part of the deep web that you can’t access through your regular browser.
This is because dark web content is hidden on purpose.
Sure, so is most deep web content – but the dark web goes the extra mile.
Deep web sites still use regular TLDs (Top-Level Domain names) like .com or .net.
Parts of the site might belong to the clear web, while others – hidden behind a login screen – are on the deep web.
Dark web sites, on the other hand, almost always use the .onion TLD.
And their domain names can look like gibberish, too.
For example, here’s what the dark web version of Facebook’s v3 Onion URL looks like:
And like the deep web as a whole, the dark web is also a vital part of the internet.
There are several legitimate uses for the dark web.
Using the Facebook dark web site as an example again, it exists so people in countries where Facebook is censored can still access a part of the free internet.
Just as important, the dark web is how whistleblowers like Edward Snowden contact journalists to leak important information safely and anonymously.
Of course, there’s a dark side to everything – including the dark web (pun intended).
Cybercriminals and even regular criminals also use the dark web to conduct illegal activities.
This ranges from selling drugs and malware to human trafficking and child pornography.
You’ll even find hackers and assassins for hire on the dark web (though 99.999% of them are scams).
However, while the illegal side is a relatively small part of the dark web, it’s best to stay away from that side altogether.
How to Stay Safe on the Dark Web?

We covered all the basics already, like choosing, setting up, and using a VPN and the Tor Browser.
But the basics alone aren’t enough to stay safe on the dark web!
Just like there are privacy and security best-practices for using the surface web, there are some dos and don’ts for browsing the dark web.
Let’s discuss.
1. Before You Connect to Your VPN, Have These Safety Precautions in Place
If you’re using Windows, macOS, Android, or iOS to access the dark web, there are a lot of extra safety precautions you need to enact before even connecting to your VPN.
You don’t have to follow these precautions before using your VPN every time, though you can do so.
But, at the very least, follow them when getting ready to browse the dark web:
- Close everything on your device, such as your password manager, regular browser, and non-essential apps like Netflix. On your smartphone, make sure to stop all background apps from running, too.
- Windows, macOS, and iOS almost always have cloud-syncing turned on by default. If you’re logged in to your Google Account on your Android, then the same might be true as well. Log out of everything you can and turn cloud-syncing off altogether.
- Cover your webcam (true for Linux as well). If you don’t have a webcam cover (they’re cheap), use a piece of paper or electric tape.
- Make sure your antivirus software is running the latest update. Even better if your antivirus also has antimalware features! As always, make sure you’re using a reputable service like Malwarebytes.
- Turn your device’s location settings off and erase location history. On your smartphone, you’ll also want to go through every app’s settings individually to deny location access as an extra precaution.
Remember to follow these steps even before you open your VPN app, let alone start browsing the dark web!
OPTIONAL – Use a Live OS in a Virtual Machine
If you want to go the extra mile with your safety precautions, I recommend using a Virtual Machine (VM) with a live operating system.
Start by installing a hypervisor – I prefer VirtualBox.

For a live operating system, the most common options are TailsOS, QubesOS, and Whonix.
You can even integrate Whonix into your QubesOS VM for better anonymity – both TailsOS and Whonix run everything through the Tor Network.
One thing to keep in mind is if you’re using a live operating system, you don’t want to use a VPN at the same time.
It’s ironic, but your VPN account becomes a potential identifier.
I consider using a live OS in a VM to be for advanced users.
Ideally, you still want to use a VM – but you can run your favorite Linux distribution in it instead of Windows or a live OS.
2. Safety Precautions for Using the Tor Browser
You already know how to properly set up and configure your Tor Browser for browsing the dark web.
But there’s one more essential safety precaution to follow (plus an optional one).
When you launch the Tor Browser, you’ll notice it doesn’t open in full-screen mode.
Instead, the browser window is much smaller – about two-thirds of your screen size at most.

Do not maximize the window!
Leave Tor Browser in its minimized mode.
This makes it infinitely more difficult for attackers stalking the dark web to figure out your screen resolution, which can be used to identify you.
Optionally, you can also make it more difficult to analyze your typing patterns by never typing anything directly in Tor.
Instead, keep a writing app open (like Notepad for Windows) and type everything there before copy-pasting it in Tor.
3. Never Offer Any Personally Identifiable Information (PII)
When you initially set up and configure your Tor Browser, you make some changes that minimize the risk of the browser itself giving away any information that can personally identify you.
As a quick recap, this includes:
- Setting your Security Level to Safest

- Changing the default search engine from DuckDuckGo to DuckDuckGoOnion (optional, but preferable)
- Disabling HTTP Referrers in the about:config settings

- Disabling iframes in the about:config settings

If you follow the previous tip’s recommendations, you aren’t broadcasting your screen resolution or typing patterns, either.
But that’s not all!
When browsing the dark web, never enter any personal information.
If you access the same accounts via the surface web of sites like Facebook, don’t touch them on the dark web.
If you do need to create or use any dark web accounts, use dark web email addresses.
Remember, ProtonMail has a .onion domain – create a new, free account there and only use it while connected through Tor.
There are also blog sites where you might want to leave comments.
Or you might want to join Dread, the dark web equivalent of Reddit.
Use your dark web email address if prompted.
Instead of your real name, use a made-up one.
And never, ever tell anyone anything that can be used to identify you.
Not your age, not what country you’re in, not even your gender identity.
Assume everyone on the dark web is lying about who they are (even if they aren’t) and do the same (lie through your digital teeth).
4. Don’t Download Any Software
Earlier, I mentioned you could get QubesOS through its Onion site.
Ideally, you don’t want to download any software through the dark web – including QubesOS.
If you absolutely have to, then only ever do so through a Virtual Machine and make sure you scan the installation file with your antivirus and antimalware program(s) before doing anything else with them.
Remember, just as there are safe, legitimate uses for the dark web, there are also malicious parties willing to take advantage of naive users.
The software you download through the dark web is just as likely to be malware as it is to be the real thing.
(Which, to be fair, is also the case on the surface web.)
BONUS – Downloading Research Papers
In the same way that you’ll use the deep web to download research papers, you can use the dark web.
The big difference is that, after downloading a PDF through the deep web, you can safely open the document after scanning it with your antivirus and antimalware programs.
Any links in the PDF will almost certainly be safe to follow.
That’s not the case with the dark web.
Wait until after you finish browsing the dark web and shut everything down again before opening any research papers you downloaded.
If you click on a link in a PDF, it’ll take you through your regular browser – and if you’re still connected to the dark web, that can identify you!
5. Don’t Buy Anything on the Dark Web (And When You Do, Be Safe)
First, a quick caveat.
There are legitimate reasons to pay for something on the dark web.
For example, if you’re upgrading your ProtonMail account from the free version to a premium subscription (though, again, only do this for the email address you create and use exclusively through ProtonMail’s Onion site).
However, in general, unless you’re 100% sure the service is legitimate, or the product you’re buying is legally sourced, don’t buy anything on the dark web.
This is another case of “safe rather than sorry.”
But if you are going to buy something through the dark web, make sure all transaction-related communication happens through your dedicated, anonymous email address.
And make sure that PGP (Pretty Good Privacy) encryption is in place.

Finally, don’t ever log into your bank account through the dark web!
Don’t even do transactions for dark web purchases through your bank account outside of the dark web.
Always use cryptocurrencies for dark web transactions.
Bitcoin is not private by default.
However, you can legally purchase Bitcoin from a reputable exchange on the surface web (such as Coinbase or Kraken) and then send it to your hardware wallet through a Bitcoin mixer.
I can recommend a few hardware wallets: Ledger (Nano X or Nano S) and Trezor (Trezor One or Trezor Model T).
Always make sure to buy your hardware wallet directly from the manufacturer’s official sites!
For a dark web wallet, I recommend Hidden Wallet (that’s a .onion link – don’t click it unless you’re using your VPN and Tor Browser!).
Hidden Wallet automatically sends your Bitcoin through a mixer, with a flat network fee of 0.001 BTC.
Don’t send your Bitcoin from the exchange platform to your dark web wallet.
Always go through your hardware wallet!
6. Don’t Take Everything You See Seriously
For the most part, what I mean is “don’t take anything at face value.”
Following the principle of “safe rather than sorry,” assume every site you encounter on the dark web is a phishing site designed to steal your personal data and/or money.
At least, assume so until proven otherwise.
If you’re ever in doubt as to whether you have the right .onion URL for a site or service you also use through the surface web (like ProtonMail), then make sure you got the URL from their surface website first.
You can even do so in the Tor Browser itself!
I also mean “don’t take everything you see seriously” in the literal sense.
Just like on the surface web, people on the dark web aren’t always who they say they are or appear to be.
Take claims and promises with a massive heap of salt.
That said, if you’re on a dark web website and someone is offering illegal content like child pornography, report it to the authorities!

The dark web exists as a safe place for whistleblowers to contact journalists and for people in dictatorial regimes to access censored information anonymously.
Illegal activities damage the dark web’s reputation, even though they’re only a small part of what happens on the dark web.
Reporting any illegal content you come across is a small but important way for you to help combat the negative stereotype that privacy is only for criminals.
7. Close Everything When You’re Done
Last but not least, make sure you close everything when you’re done.
Your first step is to close your Tor Browser tabs and then the Tor Browser itself.
I prefer to use the “New Identity” feature by clicking the icon that looks like a broom in the top-right of the Tor Browser’s toolbar.
Using this feature will close all of the tabs you have open and restart the Tor Browser.
Once it’s restarted, I close it again.
Next, if I’m using a VM with Linux, I restore it to a snapshot of the fresh installation.
This gets rid of any files you downloaded – and, more importantly, any viruses, malware, and cookies.
Then I’ll power off my VM guest OS before closing the hypervisor.
If I’m using a live OS like Tails, this isn’t necessary.
The whole operating system resets itself entirely by default, so all you have to do is shut the VM down and close your hypervisor.
Not using a virtual machine?
After closing your Tor Browser, disconnect from your VPN before rebooting your device.
What’s the Best Way to Find Dark Web Sites?
The best way to find dark web websites is to use an aggregator site.
These are sites that host .onion links with the name of the website and a short explanation of what you’ll find there.
I’m partial to two such sites: The Hidden Wiki and Daniel.

Remember – those are Onion sites, so you should only follow the links from the Tor Browser with your VPN connected!

And remember to use discretion and common sense when using aggregator sites.
They don’t only list legitimate dark web websites; they also list the illegal stuff.
Another way to find dark web websites is to check your favorite surface sites first.
Many have .onion sites as well, which they’ll mention and provide the correct Onion link to.
Here are a few quick examples I mentioned throughout this guide:
Those links are to the surface web versions, so it’s safe to click them in any browser.
What Is the Tor Over VPN Method?
In this guide, I showed you how to connect to your VPN before launching the Tor Browser (which connects you to the Tor Network).
This is called the Tor Over VPN method.
Or to borrow the name of NordVPN’s special feature, Onion Over VPN.
The Tor Over VPN method means your internet traffic goes through your VPN before entering the Tor Network.
This is the most common option.
It’s also my preferred method because it stops your ISP from seeing that you’re using Tor at all and lets you browse .onion sites normally.
The main catch is that you have to trust your VPN provider.
All three providers I recommended above use RAM-only servers that prevent logging and have a proven no-logs policy.
However, there’s a possibility that you get a malicious exit node.
All of Tor’s nodes are run by volunteers.
Statistically, it’s impossible not to end up with at least some of those nodes being run by volunteers who take advantage of the system to steal personal information.
Or they might inject malicious code into your traffic to infect your device.
This works because your traffic is decrypted when it exits the final node.
Protecting yourself from malicious exit nodes is why I strongly advise making sure you have a reputable, updated antivirus and antimalware program.
It’s also another reason you should never enter personal information anywhere while browsing the dark web.
What About VPN Over Tor?
There’s a second method: VPN Over Tor.
This time, you connect to the Tor Network first and then to your VPN.
The Tor Project doesn’t recommend using the VPN Over Tor method – and neither do I.
The VPN Over Tor method means your ISP can immediately see that you’re using Tor, so you can’t visit .onion sites and browse the dark web.
You also have to make sure you sign up for your VPN using an anonymous email and fake name and pay using anonymous methods like cryptocurrency (remember to send your Bitcoin through a mixing service first).
Otherwise, your VPN connection can be used to identify you more easily than when using the Tor Over VPN method.
In my opinion, you’re better off using Tor Over VPN instead of VPN Over Tor.
It’s easier and – so long as you practice good cyber hygiene and never enter any personal information in the Tor Browser – safer.
What Is the Best Dark Web Search Engine?
The best dark web search engine is DuckDuckGoOnion – though this only offers surface web results.
For web results that only include .onion sites, Ahmia is my preferred dark web search engine.
Ahmia’s v3 Onion URL is:
Other well-known but potentially dangerous dark web search engines include Torch, Onionland, Virtual Library, and Onion URL Repository.
FAQ
Is the Dark Web Illegal?
In most countries, it’s legal to access the dark web and use the Tor Browser.
The most notable exception is China.
However, there are illegal sites and content on the dark web, like child pornography and black markets, and partaking in those sites/content is illegal no matter your reason.
Is the Dark Web Safe?
Yes, the dark web is safe – relatively speaking.
Just like the surface web, there’s always the danger of accidentally downloading malware or falling for a phishing scam.
This is why it’s essential to use common sense and a reputable VPN when browsing the dark web with Tor.
However, if you purchase anything illegal, be warned that the authorities can trace most transactions.
Can I Access the Dark Web on iOS or Android?
Yes, you can access the dark web on iOS or Android.
You’ll need to use a VPN and the Onion Browser (iOS) or Tor Browser (Android).
However, accessing the dark web from a smartphone is not as safe as doing so from a computer, especially if you also use a Virtual Machine and live operating system on your desktop or laptop.
What Can You Find on the Dark Web?
You can find almost anything on the dark web, including private email services like ProtonMail and regular news sites like ProPublica.
However, you can also find a lot of illegal content, such as Malware-as-a-Service (MaaS), drugs and firearms, human trafficking, child pornography, and hackers and hitmen for hire.
Consider yourself warned!
Is the Dark Web Worse Than the Deep Web?
The dark web is not worse than the deep web or even the surface web – and neither of those is worse than the dark web, either.
Most of the bad reputation the deep and dark webs get is due to media sensationalism highlighting the illegal sites.
But they ignore the fact that most cybercrime actually happens on the surface web!
Who Is the Creator of the Dark Web?
No one is really the creator of the dark web – it’s just a hidden network requiring special tools to access.
That said, you could argue that the US Government created the first dark web, which was later split into MILNET for military use and ARPANET for civilian use and became the regular internet.
What Is the Hidden Wiki?
The Hidden Wiki is like Wikipedia for the darknet, and its primary use is as an aggregator site where you can find .onion links to darknet sites.
Like Wikipedia, the Hidden Wiki can also be edited anonymously by registered users.
However, unlike Wikipedia, the Hidden Wiki has both legit sites and illegal content, so be wary when browsing it.
What Is DuckDuckGo?
DuckDuckGo is a privacy-first search engine.
You can use DuckDuckGo in any browser – I actually recommend replacing Google with DuckDuckGo!
It’s also the default search engine for the Tor Browser, though they also have a dark web version you can use with Tor instead.
Is It Free to Browse the Dark Web?
Yes, it’s free to browse the dark web – other than your internet bill, of course!
However, to browse the dark web safely, you’ll want to pay for a reputable VPN.
At the same time, be cautious of anyone claiming to offer paid dark web services, no matter what they are.
Final Words

Congratulations – you now know how to browse the dark web on any device safely!
As a quick recap, remember the following basics for browsing the dark web:
- Always use a safe, reliable VPN.
- Download and install the Tor Browser from the official Tor Project website. For iOS, you’ll need to go through the Onion Browser site.
- Always connect to your VPN before opening your Tor Browser.
- Never enter any personal information or visit illegal dark web websites.
- Always close everything when you’re done browsing the dark web.
- Accessing the dark web on a computer through a virtual machine (ideally with a live operating system like Tails) is much safer than iOS or Android.
Are you ready to start browsing the dark web?
In closing, please consider sharing this article to help spread awareness that the darknet is nothing to be afraid of.
In fact, it’s vital for whistleblowers like Edward Snowden, who help promote our right to online privacy!